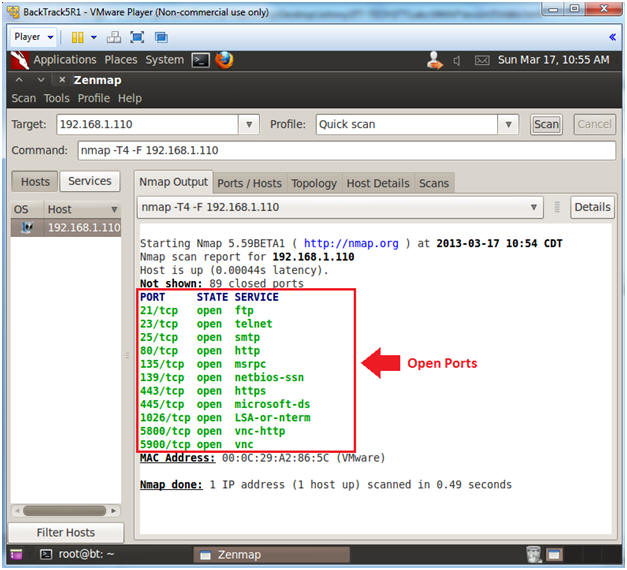
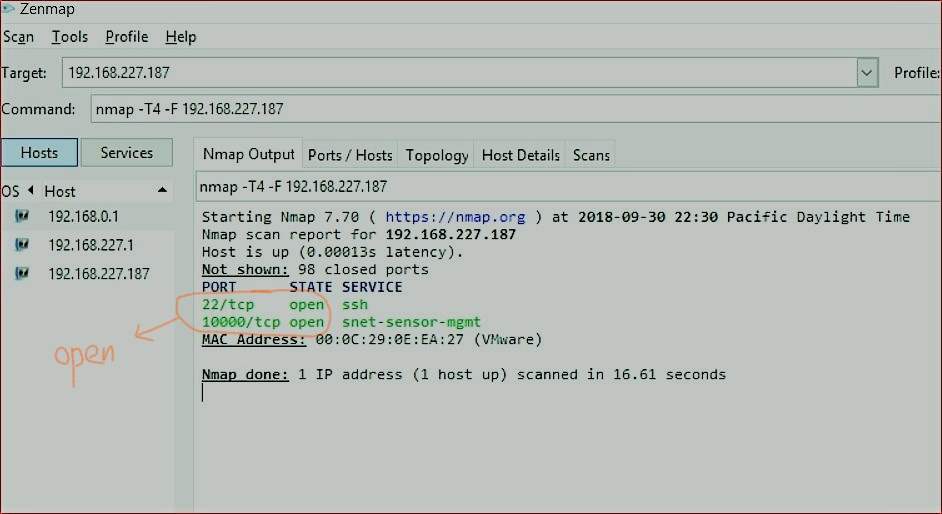
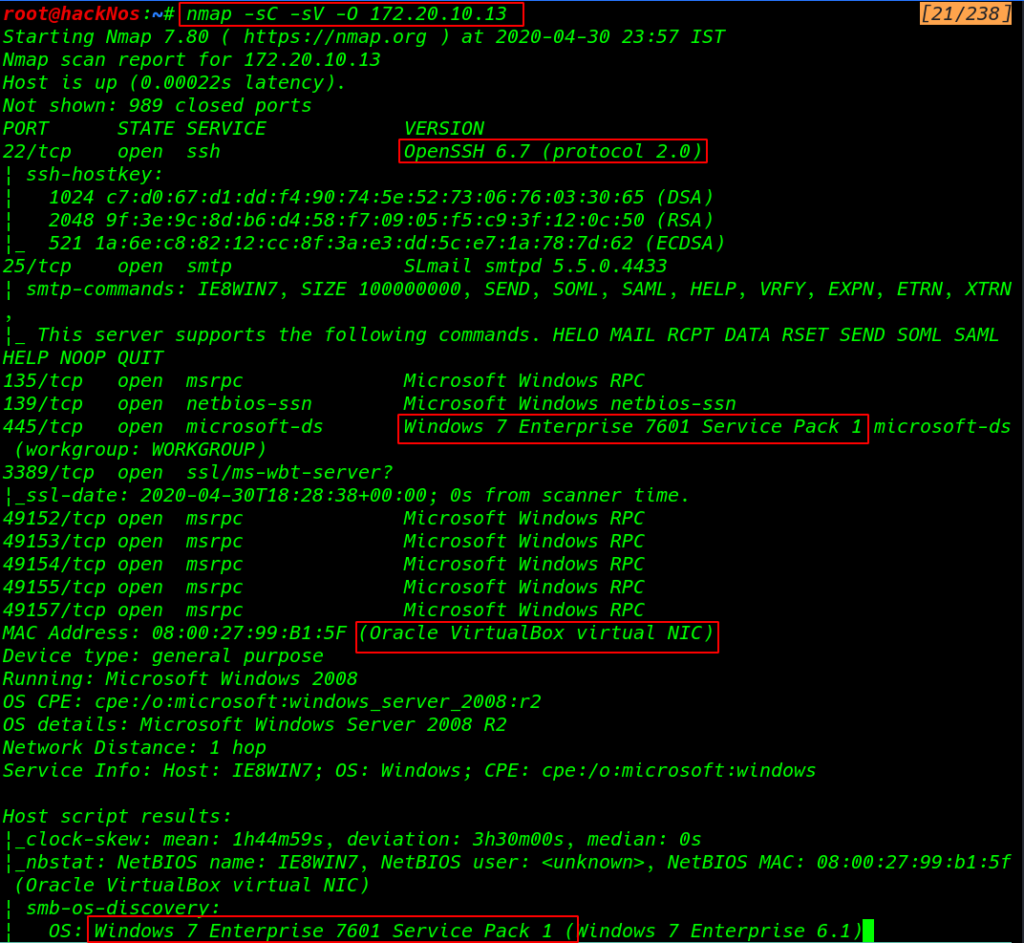
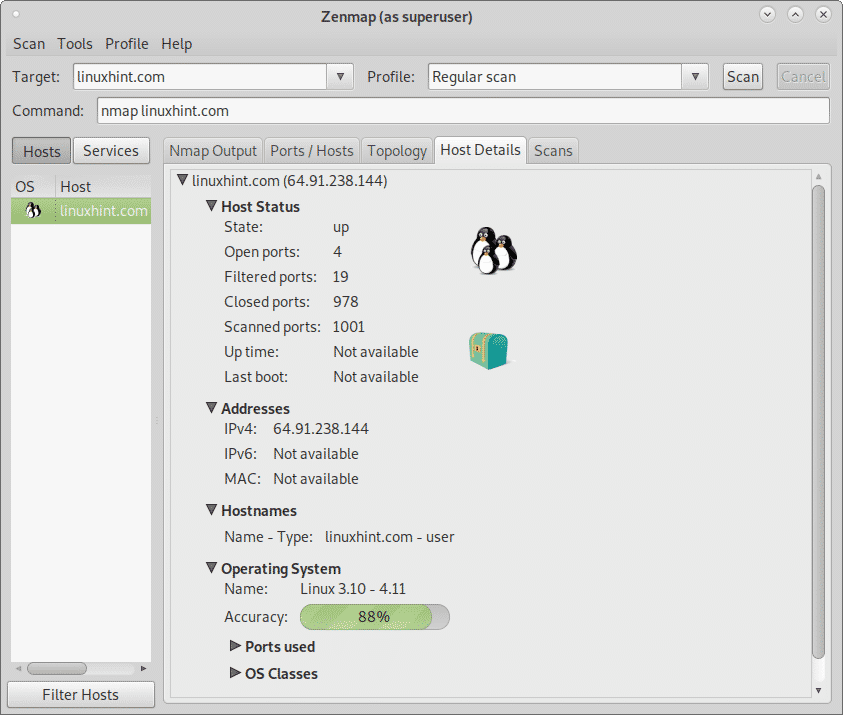
Zenmap is an free and open source GUI designed to be used with nmap.Zenmap is multiplatform tool which supports Linux, Ubuntu, Mint, Kali, Fedora, CentOS., Windows, Mac OS X, BSD etc. Nmap is very powerful tool for network scanning and vulnerability discovery but it is completely command line based.Zenmap can be used by novice users to scan network and discover vulnerabilities.
- Download Zenmap - You can easily track the network activity, as well as the traffic on a specific website, based on the available hosts, with this application.
- This command will scan your network from 192.168.0.1 to 255 and will display the hosts with their MAC address on your network. In case you want to display the mac address for a single client, use this command make sure you are on root or use 'sudo' sudo nmap -Pn 192.168.0.1 this command will display the host MAC address and the open ports.
Looking for an alternative tool to replace Zenmap? During the review of Zenmap we looked at other open source tools. Based on their category, tags, and text, these are the ones that have the best match.
Top 3
- portSpider (network vulnerability scanner)
- Masscan (high-performance port scanner)
- Nmap (network and vulnerability scanner)
These tools are ranked as the best alternatives to Zenmap.
Alternatives (by score)
portSpider
Introduction
portSpider is a security tool to scan network ranges and find open ports. The goal of the tool is to find vulnerable services.Project details
portSpider is written in Python.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Network scanning
- Vulnerability scanning
Zenmap Scan For Mac Address
Masscan
Introduction
Masscan can be compared with other tools like Nmap. Due to its focus on high performance, this tool can be used when many systems have to be scanned at once. It can scan all internet hosts on IPv4 within 5 minutes. This impressive statistic makes the tool loved by those that do security research.
Project details
Masscan is written in C.
Strengths and weaknesses
- + More than 25 contributors
- + More than 8000 GitHub stars
- + The source code of this software is available
Typical usage
- Network scanning
Nmap
Introduction
Nmap is short for 'Network Mapper'. It is a free and open source utility for network discovery and security auditing. It was release in September of 1997 by Gordon Lyon, commonly known under his pseudonym 'Fyodor'.
Project details
Nmap is written in C, C++, Lua, Python.
Strengths and weaknesses
- + Project is mature (10+ years)
- + The source code of this software is available
- + Well-known author
- + Well-known tool
- - Software usage is restricted (e.g. commercially)
Typical usage
- Network scanning
- Vulnerability scanning
QuickScan
Introduction
Although there are many port scanning utilities, sometimes it is specific functionality that makes a tool really powerful. For example, QuickScan saves the results of a scan, which then can be processed later for follow-up.
Project details
QuickScan is written in Python.
Strengths and weaknesses
- + Very low number of dependencies
- + The source code of this software is available
- - No releases on GitHub available
- - Full name of author is unknown
Typical usage
- Network scanning
DMitry
Introduction
This small utility can retrieve information from the WHOIS database, to see who owns an IP address or domain name. Besides that, it can obtain information from the system itself, like the uptime. DMitry also has the option to search for email addresses, perform a TCP port scan, and use modules specified by the user.
Project details
DMitry is written in C.
Strengths and weaknesses
- + The source code of this software is available
Cutter
Introduction
Cutter is a graphical user interface for radare2, the well-known reverse engineering framework. It focuses on those who are not familiar enough with radare2, or rather have a graphical interface instead of the command-line interface that radare2 provides.
Project details
Cutter is written in C++, Qt.
Strengths and weaknesses
- + More than 50 contributors
- + More than 3000 GitHub stars
- + The source code of this software is available
Typical usage
- Binary analysis
- Malware analysis
- Reverse engineering
IVRE
Introduction
IVRE is a framework to perform reconnaissance for network traffic. It leverages other tools to pull in the data and show it in the web interface.Project details
IVRE is written in Python.
Strengths and weaknesses
- + More than 10 contributors
- + More than 1000 GitHub stars
- + The source code of this software is available
Typical usage
- Digital forensics
- Information gathering
- Intrusion detection
- Network analysis
Pyersinia
Introduction
Pyersinia is a tool like Yersinia and can perform network attacks such as spoofing ARP, DHCP DoS , STP DoS, and more. It is written in Python and uses Scapy.Project details
Pyersinia is written in Python.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Network analysis
- Penetration testing
- Security assessment
Wireshark
Introduction
Wireshark is a mature project with many users all over the world. Its library is stable and can be used by both graphical as text-based interfaces. With many books and even conferences around the subject, this tool is a safe bet to have in your toolbox.
Project details
Wireshark is written in C.
Strengths and weaknesses
- + The source code of this software is available
- + Well-known tool
Typical usage
- Network analysis
- Network traffic analysis
- Security assessment
- Troubleshooting
Leviathan Framework
Introduction
Leviathan is a security tool to provide a wide range of services including service discovery, brute force, SQL injection detection, and exploit capabilities. The primary reason to use this tool is to do massive scans on many systems at once. For example to include a huge network range, country-wide scan, or even full internet scan.
Project details
Leviathan Framework is written in Python.
Strengths and weaknesses
- + More than 500 contributors
- + The source code of this software is available
Typical usage
- Penetration testing
- Security assessment
- Service exploitation
Portspoof
Introduction
Portspoof is a small utility with the goal to make port scanning by other much harder. It achieves this by showing all configured TCP ports to be in the 'open' state instead of closed or filter. The related ports are also emulating valid services. This way a port scan on the system will reveal many open ports and look to have legitimate services running.
Project details
Anchore
Introduction
Anchore is a tool to help with discovering, analyzing and certifying container images. These images can be stored both on-premises or in the cloud. The tooling is mainly focused on developer so that perform analysis on their container images. Typical actions include running queries, creating reports, or set up policies for a continuous integration and deployment pipeline.
Project details
Anchore is written in Python.
Strengths and weaknesses
- + More than 10 contributors
- + Commercial support available
- + The source code of this software is available
Typical usage
- System hardening
Archery
Introduction
Archery is a tool that helps to collect data about vulnerabilities within an environment. Instead of focusing on the actual scanning, it allows managing findings in a web-based interface. This includes options like reporting, searching, and dashboards. It can interact with other tools, including the well-known vulnerability scanners.
Project details
Archery is written in Python.
Strengths and weaknesses
- + More than 500 GitHub stars
- + The source code of this software is available
Typical usage
- Penetration testing
- Vulnerability management
- Vulnerability scanning
- Vulnerability testing
AutoNessus (autonessus)
Introduction
This tool is useful to time scans, for example by having it run outside of business hours, and stop when the day starts.
Note: originally another tool was named AutoNessus. That is now Seccubus.
Project details
AutoNessus is written in Python.
Strengths and weaknesses
- + The source code of this software is available
- - No releases on GitHub available
Typical usage
- Vulnerability scanning
CMSeeK
Introduction
CMSeeK is a security scanner for content management systems (CMS). It can perform a wide range of functions starting from the detection of the CMS, up to vulnerability scanning. The tool claims to support over 100 different CMS tools, with extensive support for the commonly used ones like Drupal, Joomla, and WordPress.
The scans performed by CMSeeK include version detection. It can also do enumeration of users, plugins, and themes. This might be useful to see what users or components are available. The tool includes admin page discovery, file discovery, and directory listing. Anything that might be useful to a penetration test or security assessment, might be displayed.
Project details
CMSeeK is written in Python.
Strengths and weaknesses
- + The source code of this software is available
- - Full name of author is unknown
Typical usage
- Penetration testing
- Software exploitation
- Software identification
- Vulnerability scanning
Dagda
Introduction
The main reasons to use Dagda is the detection of vulnerable or malicious components within your containerized environment.
Project details
Dagda is written in Python.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Malware detection
- Malware scanning
- Vulnerability management
- Vulnerability scanning
Damn Small FI Scanner (DSFS)
Introduction
NoneProject details
Damn Small FI Scanner is written in Python.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Security assessment
- Vulnerability scanning
Damn Small JS Scanner (DSJS)
Introduction
NoneProject details
Damn Small JS Scanner is written in Python.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Penetration testing
- Security assessment
Jackhammer
Introduction
The tool uses RBAC (Role Based Access Control) with different levels of access. Jackhammer uses several tools to do dynamic and static code analysis (e.g. for Java, Ruby, Python, and Nodejs). It checks also for vulnerabilities in libraries. Due to its modular architecture, it can use several scanners out of the box, with options to add your own.
The Jackhammer project was initially added to GitHub on the 8th of May, 2017.
Project details
Jackhammer is written in Ruby.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Collaboration
- Information sharing
JoomScan
Introduction
JoomScan could be used to test your Joomla installation or during security assessments. As it has a primary focus on Joomla, it may provide better results than generic vulnerability scanners.
Project details
JoomScan is written in Perl.
Strengths and weaknesses
- + The source code of this software is available
Typical usage
- Vulnerability scanning
- Vulnerability testing
LFI Suite
Introduction
This tool is a useful addition to the pentesting toolbox of security professionals. It can help discover and exploit any local file inclusion weakness in applications. Upon success, a reverse shell can be used to get access to the system.
Project details
LFI Suite is written in Python.
Strengths and weaknesses
- + The source code of this software is available
- - Full name of author is unknown
Typical usage
- Penetration testing
- Web application analysis
Lynis
Introduction
Lynis is an open source security auditing tool that is available since 2007 and created by Michael Boelen. Its primary goal is to evaluate the security defenses of systems running Linux or other flavors of Unix. It provides suggestions to install, configure, or correct any security measures.
Project details
Lynis is written in shell script.

Strengths and weaknesses
- + More than 50 contributors
- + Commercial support available
- + More than 4000 GitHub stars
- + Used language is shell script
- + Very low number of dependencies
- + Project is mature (10+ years)
- + The source code of this software is available
Typical usage
- IT audit
- Penetration testing
- Security assessment
- System hardening
- Vulnerability scanning
Nikto
Introduction
Nikto helps with performing security scans against web servers and to search for vulnerabilities in web applications.
Project details
Nikto is written in Perl.
Strengths and weaknesses
Nmap For Mac
- + The source code of this software is available
- + Well-known tool
Typical usage
- Penetration testing
- Security assessment
- Web application analysis
OpenSCAP
Introduction
The OpenSCAP project provides a wide variety of hardening guides, configuration baselines, and tools to test for vulnerabilities and configuration issues. It uses SCAP as the protocol to store the underlying data.
Project details
OpenSCAP is written in C.
Strengths and weaknesses
- + More than 25 contributors
- + The source code of this software is available
- + Supported by a large company
Typical usage
- Security assessment
- Vulnerability scanning
OpenVAS
Introduction
OpenVAS is an open source vulnerability scanner that emerged from when Nessus became closed source in October of 2005.
Project details
Zenmap Gui For Mac
OpenVAS is written in C.
Strengths and weaknesses
- + The source code of this software is available
- + Well-known tool
Typical usage
Zenmap Download For Mac
- Penetration testing
- Security assessment
- Vulnerability scanning
Zenmap For Mac
Some relevant tool missing as an alternative to Zenmap? Please contact us with your suggestion.
